Admin
Popular

A recent report published by the Department for Business, Energy & Industrial Strategy (BEIS)...

According to a study by Tech News World, more than half of US IT and cybersecurity professionals...

Welcome to the final instalment, part 4 of our IoT security vulnerabilities blog series. As I’ve...

Remote working environments are not necessarily new to business, but are certainly fast becoming...

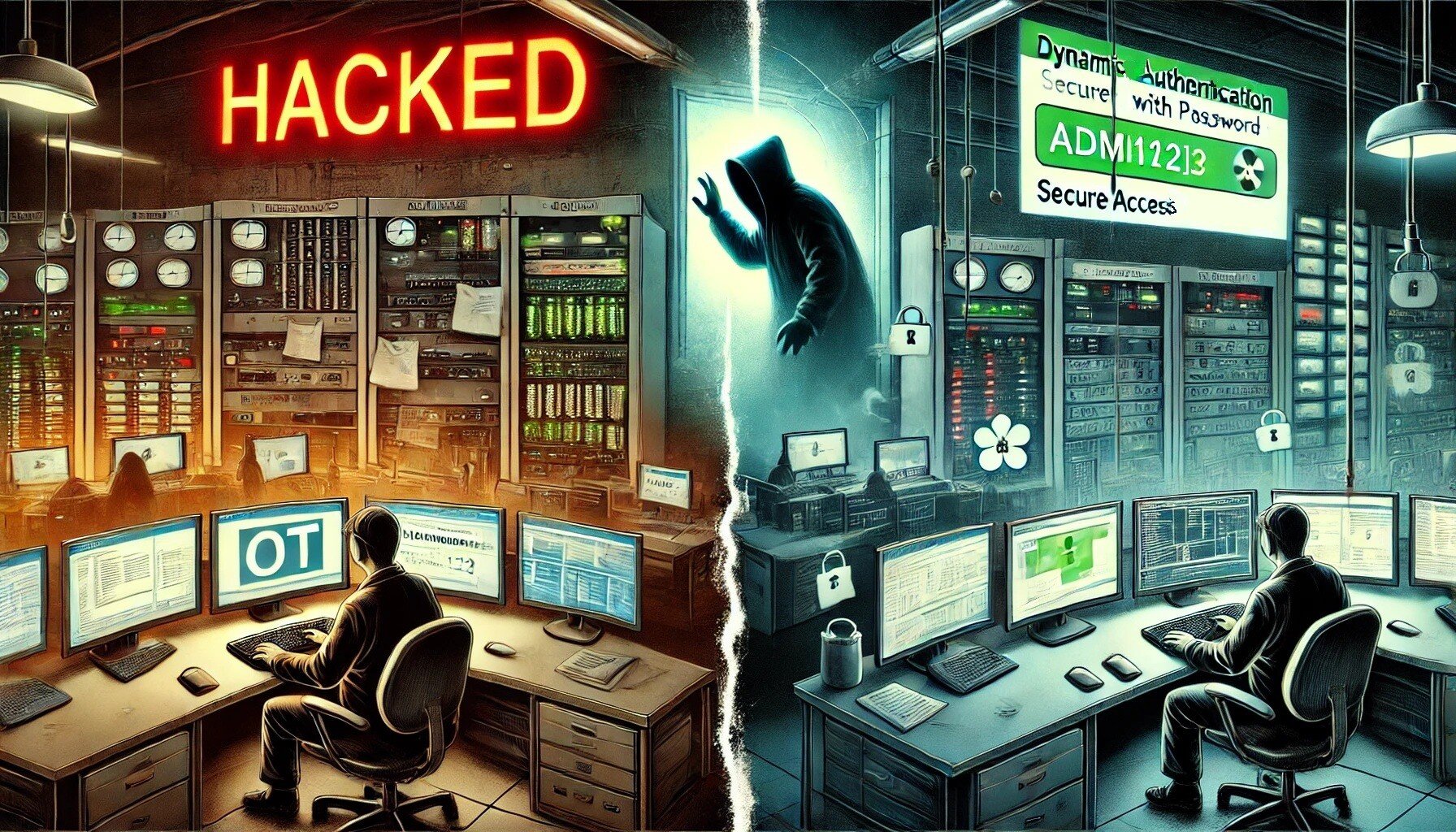
Join me, Charlie Choi, for Part 3 of our Key IoT Vulnerabilities series, with a focus on OWASP IoT...

Join me, Charlie Choi, as I once again walk you through the OWASP IoT Top 10 in the 2nd part of our...

The IoT (Internet of Things) accounts for the billions of physical devices that connect to the...

The potential benefits of drones to radically accelerate and change the landscape across multiple...

Social media hacking occurs day by day. The hackers who obtain social media account information...
In today’s rapidly changing business environment, many organisations are looking to develop...
Looking to stay up-to-date with our latest news?