Admin
Popular

Forbes notes the definition of a smart city to be ‘an urban area in which technology and sensors...

If you transfer large sum remittance at once or request sensitive financial information, most...

swIDch is going GLOBAL. Meet swIDch LIVE at one of our many upcoming exhibitions including London,...

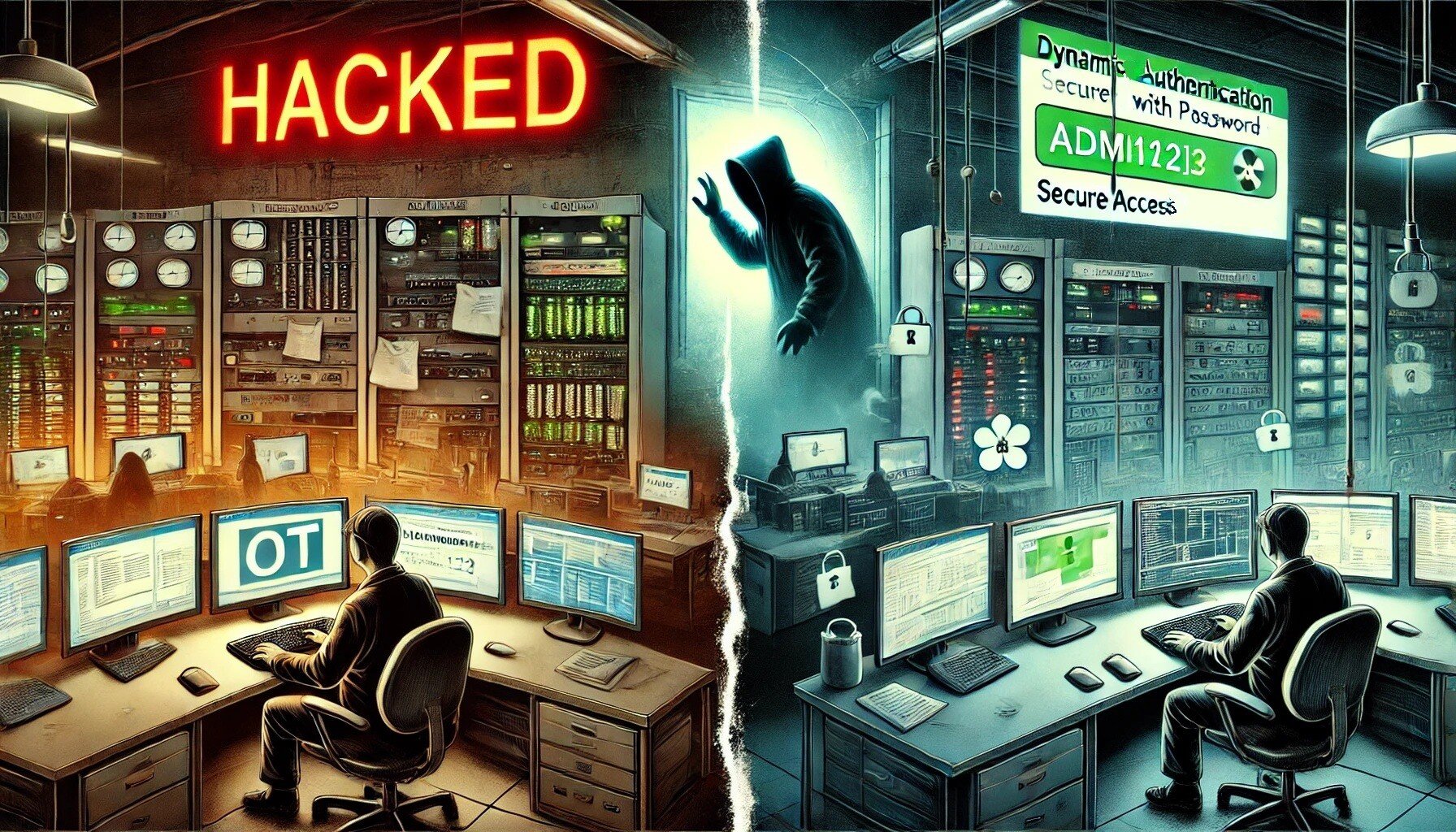
The assumption that hackers take control of the internet of things (IoT) and cause serious...

For many 2022 has been highlighted as critical in terms of IoT security, with The PSA Certified...

The quick and easy way we pay online is the most fundamental agenda of digital transformation...
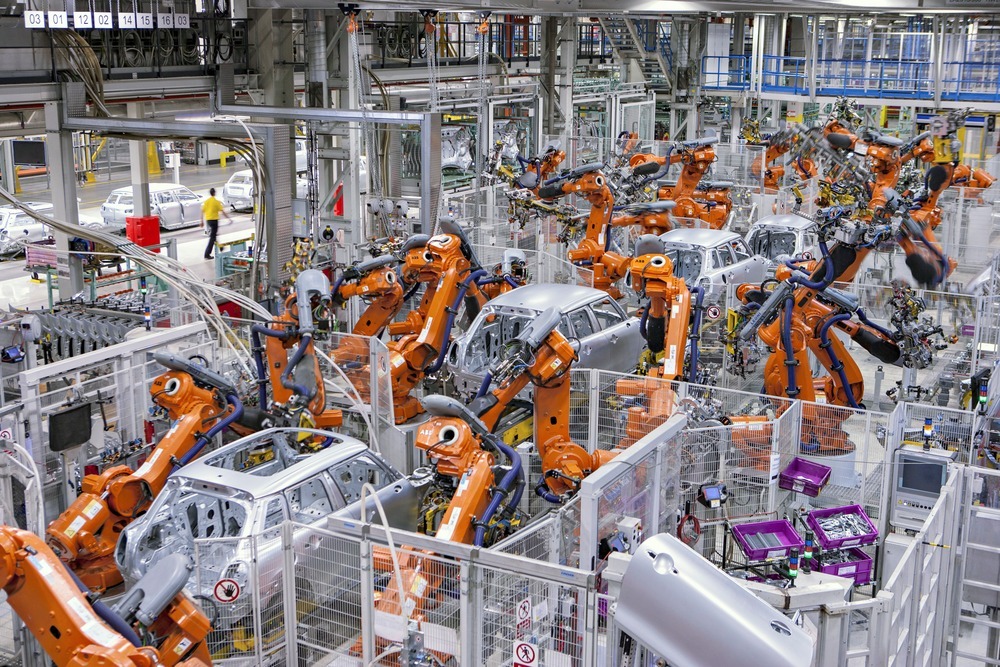
IoT provides opportunity for businesses to improve process, increase efficiency and thus...

OTAC-embedded-Smart Card will change the future of authentication in the telecom industry and...

Governments are becoming increasingly aware of the importance of IoT security, not only because of...

The world is getting smarter. As various products in our daily life are connected to the network,...
Looking to stay up-to-date with our latest news?